Step 5 — Create the RFC Connection in SAP
Step 5 — Create the RFC Connection in SAP
This guide shows how to set up the TCP/IP RFC destination that Crestone will use to communicate with your SAP system.
The RFC destination provides the secure transport channel for Crestone to execute remote-enabled function modules.
Prerequisites
- SAP GUI (SAP Logon) access to the target system/client.
- Technical user dedicated to Crestone integration with the role
ZCRESTONEassigned (see Step 4). - Hostname/IP, system number (SYSNR), client, and logon language for the SAP application server where Crestone will connect.
1) Open the RFC configuration
- Log in to SAP with a user authorized to maintain RFC destinations.
- Launch transaction
SM59(RFC Destinations). - In the navigation tree, expand TCP/IP Connections.
- Click Create (or use Display/Change → Create).
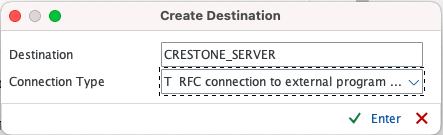
2) Maintain the RFC destination
Fill the tabs as follows:
Technical Settings
- RFC Destination:
CRESTONE_SERVER. - Connection Type: Select
T(TCP/IP Connection). - Description: Provide a short purpose (e.g., "Crestone integration").
- Activation Type: Choose
Registered Server Program. - Program ID: Set a unique identifier (e.g.,
CRESTONE_SERVER). This must match the ID configured in the Crestone connector. - Leave Gateway Host and Gateway Service with the default values for your SAP system unless BASIS specifies otherwise.
No logon credentials are required for TCP/IP destinations. Save the destination when the fields are complete.
Click Save when the fields are complete.
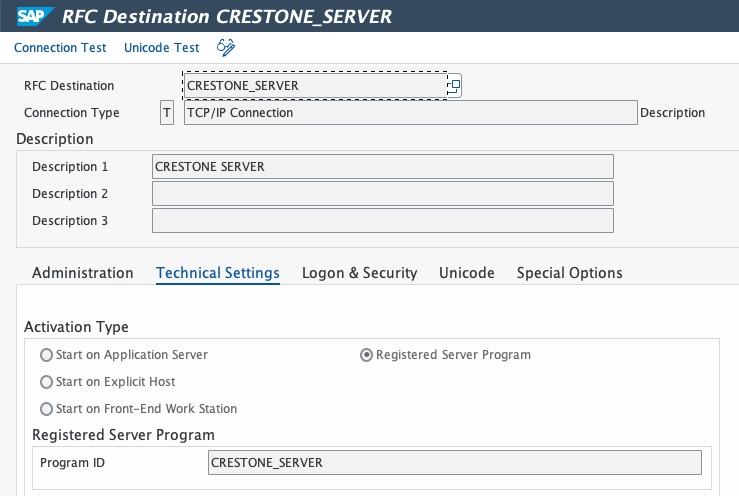
These Gateway options are essential for RFC connection with SAP. Although they are located at the bottom of the screen and require scrolling, they must be completed for the integration to function correctly.
-
Gateway Host: Here you must specify the IP address or hostname of the SAP server acting as the Gateway host. This information is critical, as it defines which SAP system the RFC service will connect to.
-
TCP Service: This value corresponds to the standard SAP Gateway service, in the format: sapgw + SAP instance number
(for example: sapgw00, sapgw01, etc.).
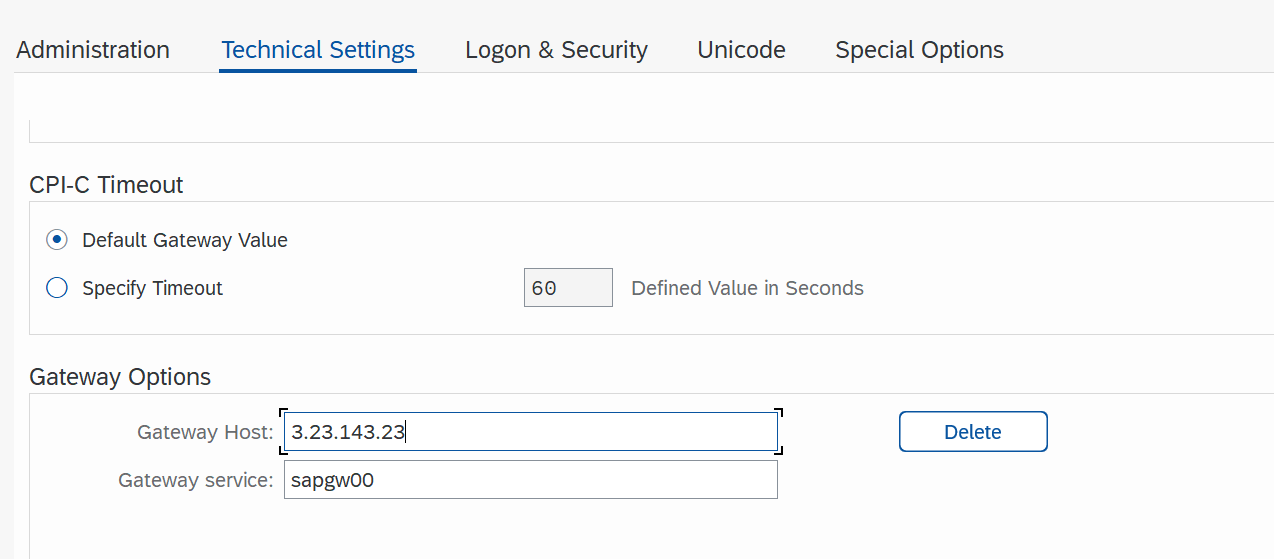
Classical serialization is recommended, as it ensures the orderly and stable processing of asynchronously transmitted data.
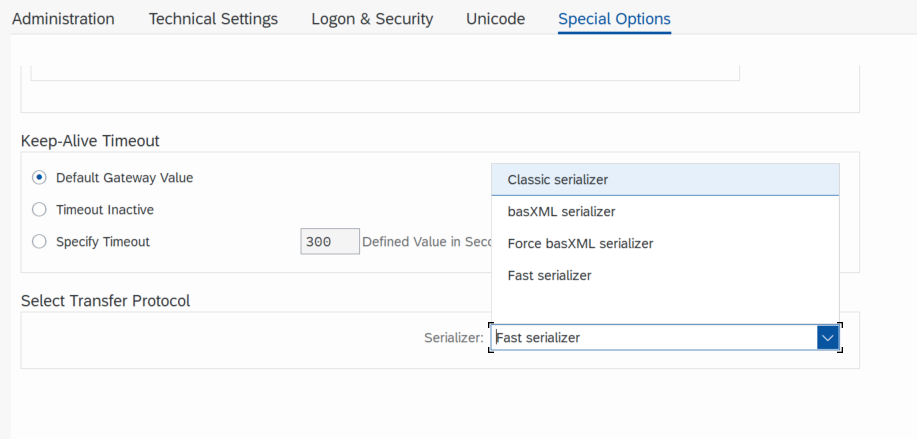
Regarding the handling of outgoing bgRFCs, the option to convert outgoing bgRFCs to outgoing qRFCs should be selected. This maintains execution order, improves queue monitoring, and facilitates error analysis during the testing and validation phase.
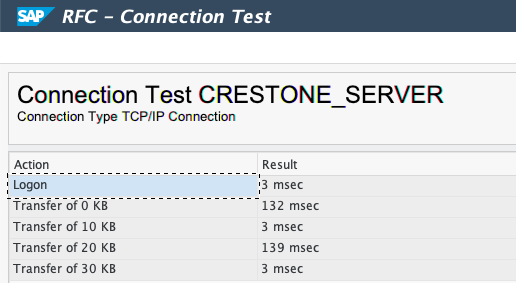
3) Test the connection
- With the new destination selected, choose Connection Test.
- Confirm you receive status Connection test OK.
- If any errors appear, verify that the Crestone connector is running and registered with the same Program ID, and confirm network/firewall settings permit the registration.
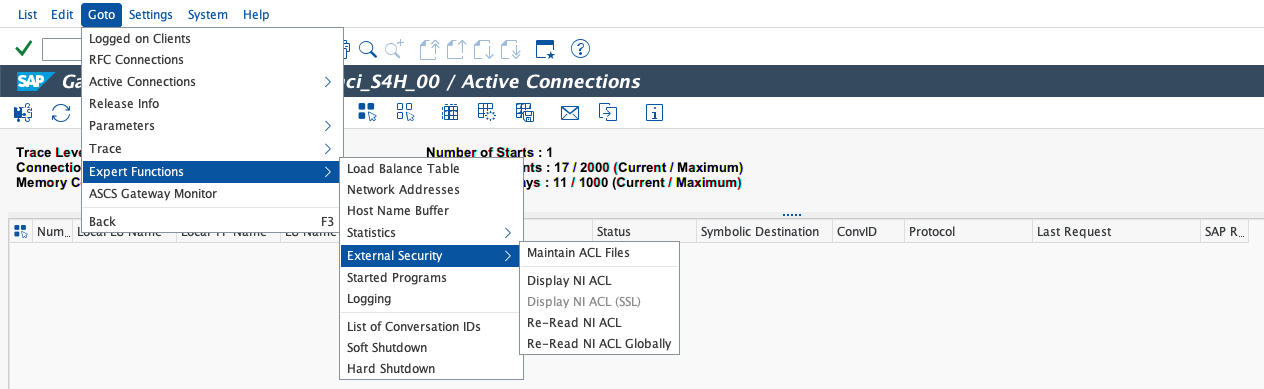
4) Configure SAP Gateway security
- Access transaction
SMGW. - Navigate to Goto ▸ Expert Functions ▸ External Security ▸ Maintain ACL Files.
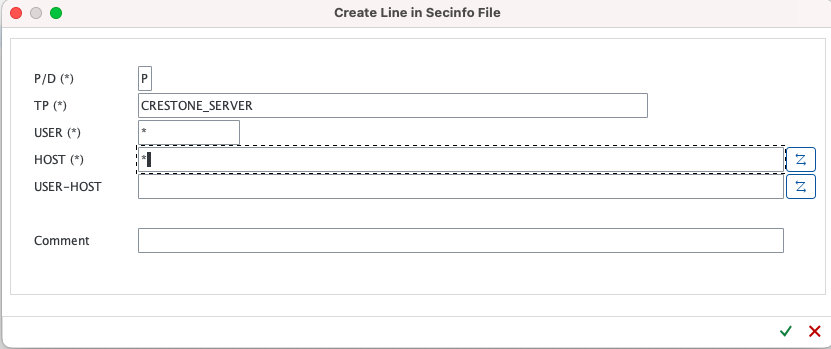
- In the secinfo file, add the standard entry that allows program
CRESTONE_SERVERto start, specifying:TP:CRESTONE_SERVERHOST: the application server host name or*(per security policy)USER: the SAP user permitted to start the program (often*for registered programs)
- In the reginfo file, add the standard entry that allows program
CRESTONE_SERVERto register from the connector host, for example:TP:CRESTONE_SERVERHOST: connector host/IPACC:*(permitted users/clients)
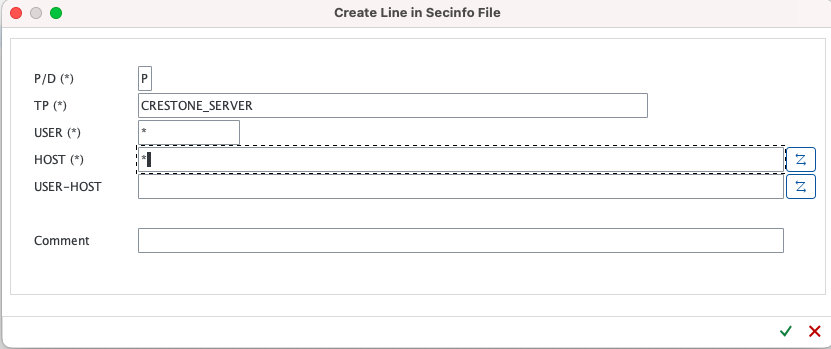
Coordinate these ACL entries with your BASIS/security team; incorrect values can block gateway registrations or expose the gateway unnecessarily.
Verification
- The RFC destination appears under TCP/IP Connections with a green status icon.
- Connection tests complete without errors.
- Logs in transaction
SM59show successful registration/test timestamps.
Summary
- Create a TCP/IP RFC destination in
SM59with connection typeT. - Set the destination name and Program ID to
CRESTONE_SERVER(or your agreed identifier). - Save and test the destination to confirm successful registration and connectivity.
- Configure SAP Gateway security